Lecture Tests
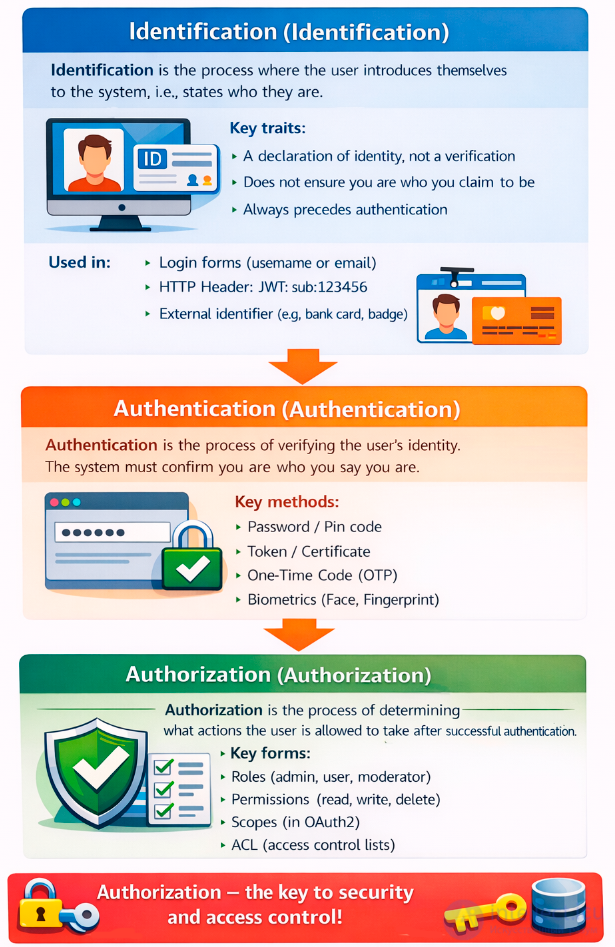
Authorization is the process that allows a user to access specific resources or system functions after successful authentication. It involves checking access rights and determining what actions the user can perform.
Authorization is the process that follows authentication.
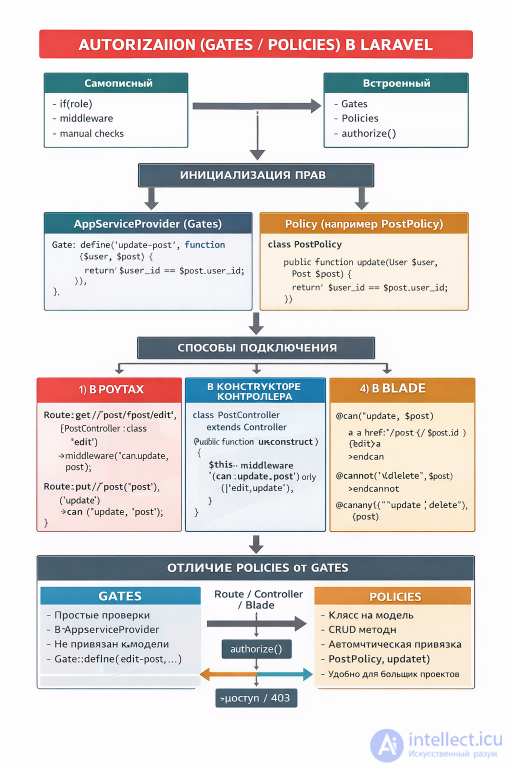
In Laravel, the authorization system is built around two key concepts: Policies and Gates.
Policies are classes that describe access rules for specific models. For example, you can define who can create, edit, or delete posts. Policies are useful when you need to associate access rights with specific database objects.
Gates are global authorization checks defined as functions. They're suitable for simple rules that aren't tied to a specific model. For example, you could create a gate that checks whether a user is an administrator.
Laravel also provides convenience methods and directives:
Thus, policies and gates allow flexible management of access to resources and actions in the application.

In Laravel, model policies are used to authorize actions on specific Eloquent model instances. A policy is associated with a model and defines methods (view, update, delete, etc.) that are automatically checked by controllers, routes, and Blade.

verification procedure
php artisan make:policy PostPolicy --model=Post
The --model=Post flag immediately associates the policy with the Post model.
The PostPolicy class will have the following methods: view, create, update, delete, restore, forceDelete.
In AuthServiceProvider:
protected $policies = [
\App\Models\Post::class => \App\Policies\PostPolicy::class,
];
Laravel will automatically pull the policy for the model.
Direct check:
public function update(Post $post)
{
$this->authorize('update', $post);
// update post
}
Resource check:
public function __construct()
{
$this->authorizeResource(Post::class, 'post');
}
Here 'post' is the name of the route parameter through which the model is retrieved.
Authorize method
public function update(Post $post)
{
$this->authorize('update', $post);
// update logic
}
Checking the policy for a specific action.
The authorizeResource method can be used to bind resource methods to a policy in the controller constructor:
public function __construct()
{
$this->authorizeResource(Post::class, 'post');
}
Now the methods index, show, create, update, delete will be checked automatically.
Use in routes
Route::delete('/posts/{post}', [PostController::class, 'destroy'])
->middleware('can:delete,post');
Middleware can check the delete policy method for the Post model.
Through middleware can
Route::get('/post/{post}/edit', [PostController::class, 'edit'])
->middleware('can:update,post');
Here the update policy for the Post model is checked.
For resource routes, you can combine it with authorizeResource in the controller to avoid manually writing middleware.
@can directive
@can('update', $post)
a href="{{ route('post.edit', $post) }}" Edit /a
@endcan
@cannot directive
@cannot('delete', $post)
p Deletion not available /p
@endcannot
@canany's directive
@canany(['update', 'delete'], $post)
p You can edit or delete the post/p
@endcanany
@can('update', $post)
a href="{{ route('posts.edit', $post) }}" Edit/a
@endcan
@cannot('delete', $post)
p Deletion is not available
| Controller method | Method of politics | Model parameter |
|---|---|---|
| index | viewAny | — |
| show | view | Post $post |
| create | create | — |
| store | create | — |
| edit | update | Post $post |
| update | update | Post $post |
| destroy | delete | Post $post |
| Place of application | Example | When to use |
|---|---|---|
| Controller | $this->authorize('update', $post) | Logic inside a method |
| Controller (resource) | $this->authorizeResource(Post::class, 'post') | Automatic verification for CRUD |
| Route | ->middleware('can:update,post') | Route-level access restriction |
| Vyukha | @can('update', $post) | Displaying interface elements |
Using Gates and Policies in Laravel to filter data by owner is a correct and recommended approach, but it's important to understand their purpose: they authorize actions, not the actual data retrieval. For filtering Eloquent queries, it's best to combine policies with query scopes or middleware.
Gates are simple conditional checks (e.g. Gate::allows('update-post', $post)).
Policies are classes associated with models that describe authorization methods (view, update, delete, etc.).
Main purpose: to allow or disallow user action on a specific model.
// PostPolicy.php
public function view(User $user, Post $post)
{
return $user->id === $post->user_id;
}
public function index()
{
$posts = Post::where('user_id', auth()->id())->get();
return view('posts.index', compact('posts'));
}
// В модели Post
public function scopeOwnedBy($query, $userId)
{
return $query->where('user_id', $userId);
}
// Использование
$posts = Post::ownedBy(auth()->id())->get();
// PostPolicy.php
public function viewAny(User $user)
{
return $user->role_id === RolesEnum::ADMIN->value;
}
// In the Post model
public function scopeOwnedBy($query)
{
if (auth()->user()->can('viewAny', Post::class)) {
return $query; // admin sees everything
}
return $query->where('user_id', auth()->id());
}
or
// PostPolicy.php
public function viewNotOwner(User $user)
{
// for example, a moderator can see other people's posts return $user->is_moderator;
}
// In the Post model
public function scopeVisibleFor($query)
{
$user = auth()->user();
if ($user->can('viewNotOwner', Post::class))
{
// the moderator sees all posts except his own
return $query->where('user_id', '!=', $user->id);
}
// a regular user sees only his own
return $query->where('user_id', $user->id);
}
But if there is a mixture of them, the code becomes less transparent: the scope begins to solve authorization problems, although its role is only filtering and is architecturally less clean.
In Laravel, policies can be used in multiple layers of an application—controllers, routes, and even views.
Filter data using scopes or query builder.
Use Policies to check access to specific actions.
Combine both approaches: first filter the selection, then check authorization.
| Approach | Pros | Cons | When to use |
|---|---|---|---|
| Politics | Centralized authorization, easy to test | They don't filter the data themselves | Checking access to a specific model |
| Scopes | Clean code, reusability | You have to remember the challenge | Filtering selections by owner |
| Middleware | Universal, you can restrict access to routes | Less flexible for complex conditions | Restricting access to entire resources |
Each question has 4 answer options.
Only one answer is correct - it is marked with an *.
After the list of answers, there is a hint briefly explaining the correct choice.
It is recommended that you first try to answer the question yourself, then check the correct answer and read the hint.
The test can be taken sequentially or selectively - it covers different aspects of authorization in Laravel.
1. What is a Policy in Laravel?
A Policy is an object-based form of authorization that checks user permissions.
2. How to create a Policy in Laravel?
The artisan make:policy command is used.
3. Where are Policies registered?
All policies are registered in AuthServiceProvider.
4. What is Gate in Laravel?
Gate is a global authorization function.
5. How do I define a Gate?
Gate is defined via Gate::define.
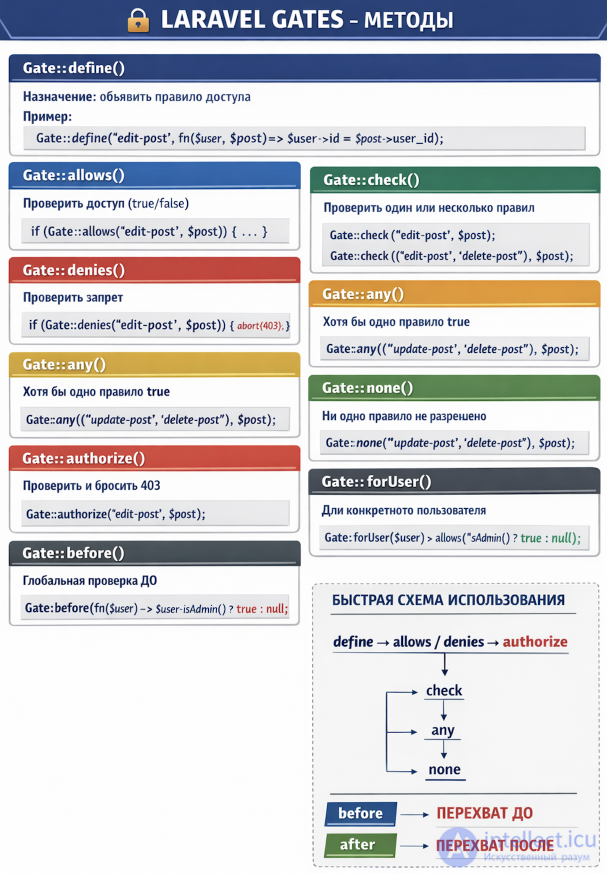
6. How do I call Gate in code?
Checking is performed via Gate::check or Gate::allows.
7. What does the authorize() method do in a controller?
authorize() calls the appropriate policy.
8. Which Policy method checks access to a specific model?
A policy typically contains methods for each operation: view, update, delete.
9. What does the Gate::allows() method return?
Gate::allows returns a Boolean value.
10. How do I associate a Policy with a model?
In the AuthServiceProvider, specify the model and policy mapping.
11. What does the can() method do for the user?
can() is a convenient method for checking authorization.
12. Which Blade directive checks permissions?
@can is used to check access permissions in templates.
13. What does the deny() method do in Policy?
deny() returns access denied.
14. Which middleware is responsible for authorization?
Can middleware checks access rights.
15. What is best to use for complex authorization logic?
For complex logic, a combination of Policy and Gate is used.
16. What does the Gate::denies() method do?
denies() is the opposite of allows(); it returns true if denied.
17. Which Policy method is used to check for model deletion?
The delete() method determines access to deletion.
18. How can I call Policy validation directly in a controller?
authorize() calls the policy method on the model.
19. What does the before() method in Policy do?
before() allows you to globally allow or deny access.
20. Which method is used for bulk viewing of models?
viewAny() checks access to a list of models.
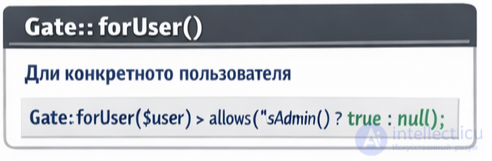
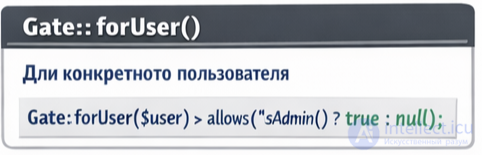
21. What does the Gate::forUser($user) method do?
forUser allows you to check the permissions of another user.
22. Which Blade directive is used to check for access denial?
@cannot is used to check prohibition.
23. What does the Gate::inspect() method do?
inspect() gives a detailed inspection result.
24. Which Policy method checks for model creation?
create() is responsible for creation access.
25. What does the Gate::authorize() method do?
authorize() throws an exception if access is denied.

26. Which Policy method checks for a model update?
update() is responsible for access change.
27. What does the Gate::abilities() method do?
abilities() returns an array of all gates.
28. Which Policy method checks the view of the model?
view() is responsible for accessing the view.
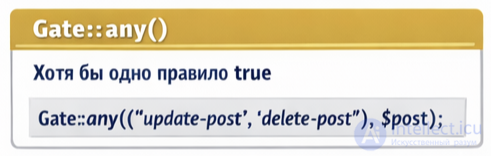
29. What does the Gate::any(['edit','delete'])?
any() returns true if at least one rule is met.
30. Which Policy method checks for model recovery?
restore() is responsible for restoring access.
31. Which Policy method checks for permanent deletion of a model?
forceDelete() is used to check for permanent deletion access.
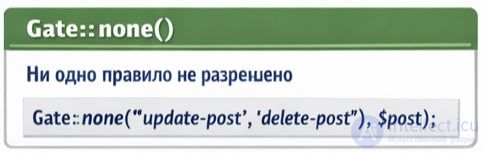
32. What does the Gate::none(['edit','delete']) method do?
none() returns true if no rule is allowed.
33. Which Policy method checks for mass deletion of models?
deleteAny() is responsible for access to mass deletion.
34. What does the Gate::after() method do?
after() allows Globally change the validation result.
35. Which Policy method validates the mass creation of models?
createAny() is responsible for access to mass creation.
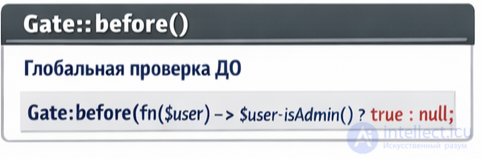
36. What does the Gate::before() method do?
before() allows you to set a global rule before all other rules.
37. Which Blade directive checks multiple permissions at once?
@canany checks for the presence of at least one permission.
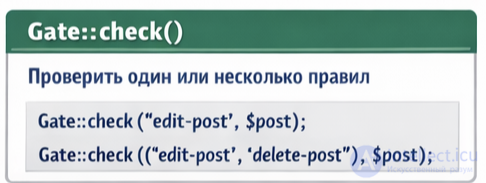
38. What does the Gate::check() method do?
check() is used to check access.
39. Which Policy method checks for mass update of models?
updateAny() is responsible for access to mass updates.
40. What does the Gate::allows() method do?
allows() returns true if access is allowed.
41. Which Policy method checks for bulk restore of models?
restoreAny() is responsible for access to bulk restore.
42. What does the Gate::authorize() method do if denied?
authorize() throws an exception if access is denied.
43. Which Policy method checks for bulk viewing of models?
viewAny() is used to check access to a list of models.
44. What does the Gate::forUser() method do?
forUser allows you to check the permissions of another user.
45. Which Policy method checks for mass hard deletion of models?
forceDeleteAny() is responsible for access to mass hard delete.
46. Which Policy method checks for mass editing of models?
updateAny() is used to check for access to mass editing.
47. What does the Gate::define() method do?
define() is used to register a new gate.
48. Which Blade directive checks multiple rules at once?
@canany checks for at least one permission.
49. What does the Gate::abilities() method do?
abilities() returns an array of all gates.
50. Which Policy method checks for mass hard deletion of models?
forceDeleteAny() is responsible for accessing mass hard deletion.
51. What does the Gate::check() method do?
check() is used to check access.
52. Which Policy method checks for mass model restore?
restoreAny() is responsible for access to mass restore.
53. What does the Gate::denies() method do?
denies() is the opposite of allows(); it returns true if denied.
54. Which Policy method checks for mass model creation?
createAny() is responsible for access to mass creation.
55. What does the Gate::none(['edit','delete']) method do?
none() returns true if no rules are allowed.
56. Which Policy method checks whether a model is viewable?
view() is responsible for access to the view.
57. What does the Gate::any(['edit','delete']) method do?
any() returns true if at least one rule is met.
58. Which Policy method checks for model deletion?
delete() determines deletion access.
59. What does the Gate::inspect() method do?
inspect() returns a detailed inspection result.
60. Which Policy method checks for a model update?
update() is responsible for access to edits.
61. What does the Gate::allows() method do if the check is successful?
allows() returns true if access is allowed.
62. Which Policy method checks for bulk editing of records?
updateAny() is used to check for bulk editing.
63. What does the Gate::authorize() method do if it is denied?
authorize() throws an exception if access is denied.
64. Which Blade directive checks permissions for a specific action?
@can is used to check access rights in templates.
65. What does the Gate::before() method do?
before() allows you to set a global rule before all other rules.
66. Which Policy method checks for bulk deletion of records?
deleteAny() is responsible for accessing bulk deletions.
67. What does the Gate::after() method do?
after() allows you to globally change the result of the check.
68. Which Policy method checks for model recovery?
restore() is responsible for access to recovery.
69. What does the Gate::forUser($user) method do?
forUser allows you to check the permissions of another user.
70. Which Policy method checks for permanent deletion of a model?
forceDelete() is used to check for access to permanent deletion.
Comments
To leave a comment
Running server side scripts using PHP as an example (LAMP)
Terms: Running server side scripts using PHP as an example (LAMP)